Frequently Asked Interview Questions on Blockchain
Introduction
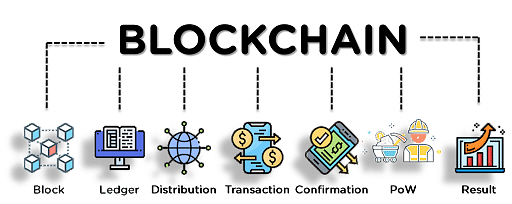
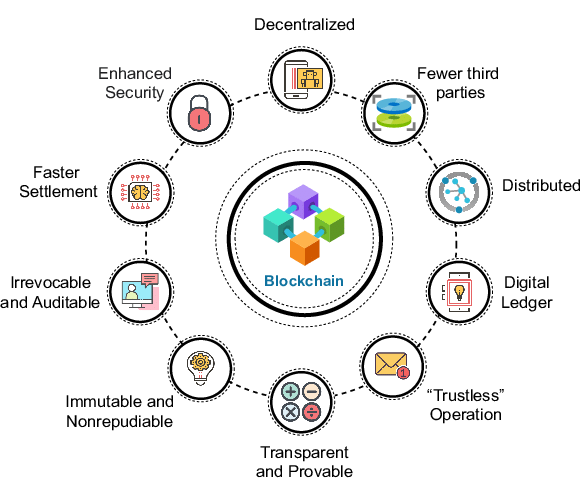
Blockchain is a decentralized digital ledger technology that records transactions across a network of computers in a secure, transparent, and tamper-proof manner. It was first introduced as the underlying technology for the cryptocurrency, Bitcoin, but has since evolved to have many other potential use cases. In a blockchain, transactions are grouped into blocks and verified by multiple nodes, creating a blockchain representing the entire transaction history. The decentralized nature of blockchains eliminates the need for intermediaries. It ensures that the data on the blockchains cannot be altered retroactively, making it an immutable and secure way to store and transfer information or assets.

Learning Objectives
- A clear understanding of blocks, the different types, and key features of blockchain
- Understanding Encryption and security of blockchain
- Merkle Trees and its application in blockchain
- A detailed idea about blockchain ledger
- The concept of double spending and its usefulness in blockchain
This article was published as a part of the Data Science Blogathon.
Table of Contents
- Beginner-Level Questions on Blockchain
1.1. What do you mean by blocks in blockchain technology?
1.2. What are the different types of blockchains?
1.3. What are the four key features of blockchain?
1.4. What is encryption, and what is its role in blockchain?
1.5. Is it possible to modify the data once it is written in a block? - Intermediate-Level Questions on Blockchain
2.1. What do you know about the security of a block?
2.2. What are Merkle trees, and how important is it in blockchains?
2.3. What is a ledger? Is blockchain an incorruptible ledger?
2.4. How is a blockchain ledger different from a shared ledger?
2.5. Explain the components of a blockchain ecosystem. - Expert Level Questions on Blockchain
3.1. What is Double Spending? Is it possible to double-spend in the blockchain ecosystem?
3.2. What kind of records can be kept in blockchain? Is there any restriction to the same?
3.3. Which cryptographic algorithm is used in blockchain?
3.4. What are the benefits of blockchain?
3.5. What do you mean by coin-base transaction? - Conclusion
Beginner-Level Questions on Blockchain
Q1. What do you mean by Blocks in Blockchain Technology?
In blockchain technology, a block refers to a unit of data containing information about network transactions. A block typically consists of several essential components, including a header containing metadata about the partnership, such as a timestamp and a reference to the previous block (creating a chain of blocks), and a list of verified transactions added to the block. Creating new partnerships and adding them to the existing chain of blocks is called “mining” and is performed by specialized nodes on the network. The blocks form a decentralized and distributed ledger of all transactions on the web, providing a secure and transparent data record.

Source: Stanford University
Q2. What are the Different Types of Blockchains?
There are mainly two types of blockchain:
- Public Blockchains are open, decentralized networks in which anyone can join and participate. Transactions are validated by a consensus mechanism, such as proof of work (PoW) or proof of stake (PoS), among the nodes in the network. Examples include Bitcoin and Ethereum.
- Private Blockchains: Also known as permissioned blockchains, these are private networks where access is restricted and controlled by a central authority. Participants in the network must be granted permission to join and validate transactions. Private blockchains are commonly used in consortiums and enterprise solutions where privacy and security are concerned.
Additionally, some blockchains can be classified based on the structure of the network and its consensus mechanism, for example:
- Proof of Work (PoW) Blockchain: These blockchains use a consensus mechanism based on solving complex mathematical problems to validate transactions.
- Proof of Stake (PoS) Blockchain: In a PoS blockchain, transactions are validated by “stakers” who hold a certain amount of the network’s native cryptocurrency.
- Federated Blockchain: Federated blockchains operate under the control of a consortium of organizations, where each organization operates a node and has an equal say in decision-making.
- Hybrid Blockchain: A hybrid blockchain combines elements of both public and private blockchains to provide the best of both worlds.
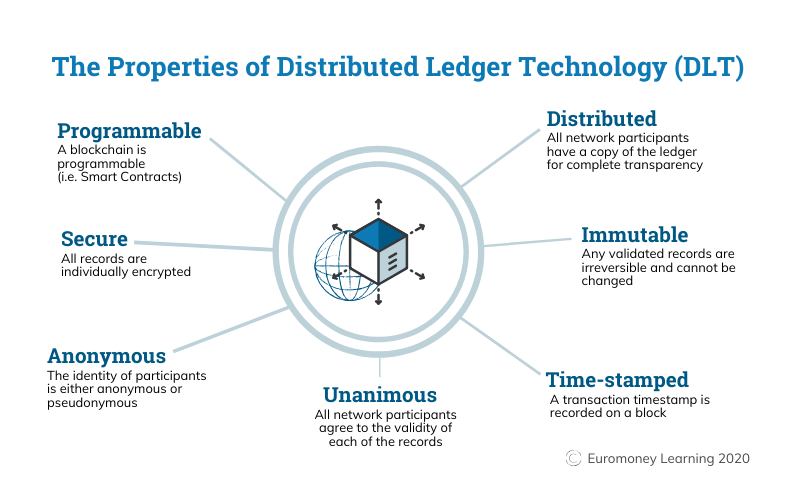
Q3. What are the Four Key Features of Blockchain?
The four key features of blockchain technology make it a suitable platform for a wide range of applications, including digital currencies, supply chain management, and secure record keeping are:
- Decentralization: Blockchains operate on a decentralized network, where multiple nodes validate transactions rather than relying on a single centralized authority.
- Immutable: Once data is recorded on the blockchain, it cannot be altered or deleted, providing a permanent and tamper-proof record of all transactions.
- Transparency: The information stored on the blockchain is visible to all participants, providing transparency and accountability.
- Security: Blockchains use cryptographic algorithms to secure the network, ensuring that transactions cannot be tampered with and providing a high level of protection to the data stored on the web.
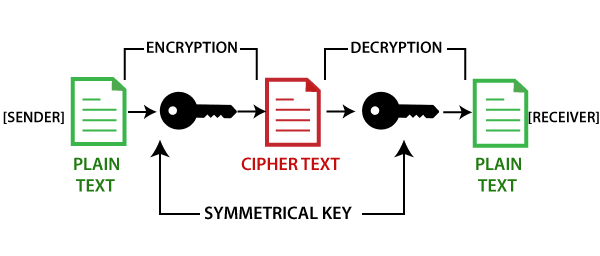
Q4. What is Encryption, and What is its Role in Blockchain?
Encryption is the process of encoding information to protect it from unauthorized access. In cryptography, encryption, and decryption are the two methods that comprise the encryption process. Encryption takes plain text as input and transforms it into an unreadable form (ciphertext) using a secret key. Decryption takes the ciphertext and the private key and converts them into plain text.
In the blockchain, encryption plays a crucial role in maintaining the security and privacy of the network. It is used to secure the data stored on the blockchain and protect the transactions’ confidentiality. For example, in public blockchains like Bitcoin, encryption is used to protect the confidentiality of transactions by encrypting the sender’s and recipient’s addresses and the amount being transferred.
Additionally, encryption is used in the consensus mechanism of many blockchains networks to ensure that blocks are valid and that the network operates in a secure and tamper-proof manner.
Q5. Is it Possible to Modify the Data Once it is Written in a Block?
It is tough to modify data once it is written in a block in a blockchain. This is due to the design of blockchain technology, which uses cryptographic algorithms to secure the network and ensure the data’s integrity.
Each block in the blockchains contain a unique digital fingerprint (hash) generated using the data in the league and the hash of the previous block in the chain. If any data in a block is altered, even a small change, it will result in a different hash being generated, which would immediately be detected by the network.
For this reason, once data is written in a block and added to the blockchain, it is considered permanent and tamper-proof. Modifying a block’s data would require changing the data in not only the block in question but also in all subsequent blocks in the chain, which would be a challenging and computationally intensive task.
However, it is possible to add new blocks to the blockchain that would effectively “overwrite” the original data, but this would require a consensus among the participants on the network to accept the changes. This makes it extremely difficult to alter the data on a well-established and secure blockchain network.
Intermediate-Level Questions on Blockchain
Q1. What do you Know About the Security of a Block?
Block security is an essential aspect of blockchain technology and is achieved through cryptographic algorithms and decentralized consensus mechanisms.
- Cryptographic Algorithms: Blockchains use cryptographic algorithms, such as SHA-256 and Scrypt, to secure the network and protect the data stored in blocks. These algorithms ensure that once a block is added to the blockchain, the data in it cannot be tampered with or altered without being detected.
- Decentralized Consensus: Blocks are added to the chain through a consensus mechanism, such as proof of work (PoW) or proof of stake (PoS). In a PoW blockchain, for example, a block is added to the chain by a node that successfully solves a complex mathematical problem, ensuring that the league is valid and that the network operates in a secure and tamper-proof manner.
- Network Size and Distribution: The larger and more decentralized a blockchain network is, the more secure it is considered to be. This is because a malicious attacker would need to control a significant portion of the network’s computing power to successfully attack the network and alter the data in a block.
Overall, the security of a block in blockchains is determined by the strength of the cryptographic algorithms used, the consensus mechanism’s reliability, and the network’s size and distribution. A secure and well-designed blockchain network can provide high security to the data stored in its blocks.
Q2. What are Merkle Trees, and How Important is it in Blockchains?
A Merkle tree, also known as a binary hash tree, is a data structure used in blockchain technology to increase the efficiency and security of verifying transactions. It is named after Ralph Merkle, who invented the concept in the 1980s.
In a Merkle tree, transactions are grouped into pairs, and a hash function is applied to each team to generate a new hash value. This process is repeated until all the transactions in the tree are grouped into a single hash value, known as the root hash.
The root hash is then included in the block header and added to the blockchain. To verify a transaction, a node can compare the hash value of the trade in question with the root hash in the block header. If the values match, the transaction is valid and has not been tampered with.
The use of Merkle trees in blockchains has several advantages:
- Efficiency: Merkle trees allow nodes to verify transactions more efficiently because they only need to compare the hash value of the trade in question with the root hash rather than all the transactions in the block.
- Security: Merkle trees increase the safety of the blockchain by making it more difficult for an attacker to alter a transaction without being detected. This is because altering a single transaction would require changing the transaction in question and all the hashes in the tree that lead to the root hash.
- Scalability: Merkle trees also help to increase the scalability of the blockchains by allowing nodes to process and verify only a portion of the transactions in a block rather than the entire block
Q3. What is a Ledger? Is Blockchain an Incorruptible Ledger?
A ledger is a record-keeping system for financial transactions or other forms of data. Logs can be kept in physical or digital formats and track the movements of assets and liabilities over time.
Blockchains are a specific type of ledger maintained across a decentralized network of computers. One of the critical features of a blockchains are that they are designed to be incorruptible, meaning that once data has been recorded on the blockchain, it cannot be altered retroactively without the network’s consensus. This makes blockchains well-suited for applications where trust and transparency are essential, such as in finance, supply chain management, and voting systems.
Q4. How is a Blockchain Ledger Different from a Shared Ledger?
A traditional ledger is a centralized record-keeping system where a single entity, such as a bank or an accounting firm, records transactions. In contrast, a blockchain ledger is decentralized, meaning that it is maintained across a network of computers, and transactions are verified and recorded by a consensus of participants in the network.
The decentralized nature of a blockchain ledger offers several advantages over traditional registers. For example:
- Immutability: Once a transaction has been recorded on a blockchain ledger, it cannot be altered retroactively without the network’s consensus. This makes it more secure and tamper-resistant than a traditional ledger, where a single entity controls the data.
- Transparency: All participants in a blockchain network have access to the same information, making it more transparent than a traditional ledger, where only the entity in charge of the roster has access to the data.
- Decentralization: Because a blockchain ledger is maintained across a network of computers, there is no single point of failure or control. This makes it more resistant to attacks and censorship than a traditional ledger.
Source: huyenchip.com
Q5. Explain the Components of a Blockchain Ecosystem.
A blockchain ecosystem comprises several vital components that maintain a decentralized ledger of transactions. These components include:
- Nodes: A node is a computer or device participating in the network. Nodes validate and process transactions and store a copy of the blockchain ledger.
- Network: The network refers to all the nodes participating in the ecosystem. It is responsible for maintaining consensus among the nodes and verifying transactions.
- Consensus Mechanism: A consensus mechanism is a process by which the network agrees on the state of the ledger. Blockchain ecosystems use other consensus mechanisms, such as Proof of Work (PoW) or Proof of Stake (PoS).
- Cryptographic Hashing: Cryptographic hashing converts data into a fixed-length, unique digital signature. Hashing is used in blockchain to secure transactions and to link them together in a chain.
- Transactions are the basic unit of data recorded on a blockchain ledger. They represent the transfer of assets or information from one user to another.
- Smart Contracts: Smart contracts are self-executing contracts with the terms of the agreement between buyer and seller being directly written into lines of code. They are used to automate the execution of transactions.
- Mining/Validating: Mining or validating is the process of verifying transactions and adding them to the blockchain ledger. In Proof of Work systems, this is done through a process called “mining,” while in Proof of Stake systems, it is done by “validators.”
These components form a secure, transparent, decentralized ecosystem for recording and verifying transactions.
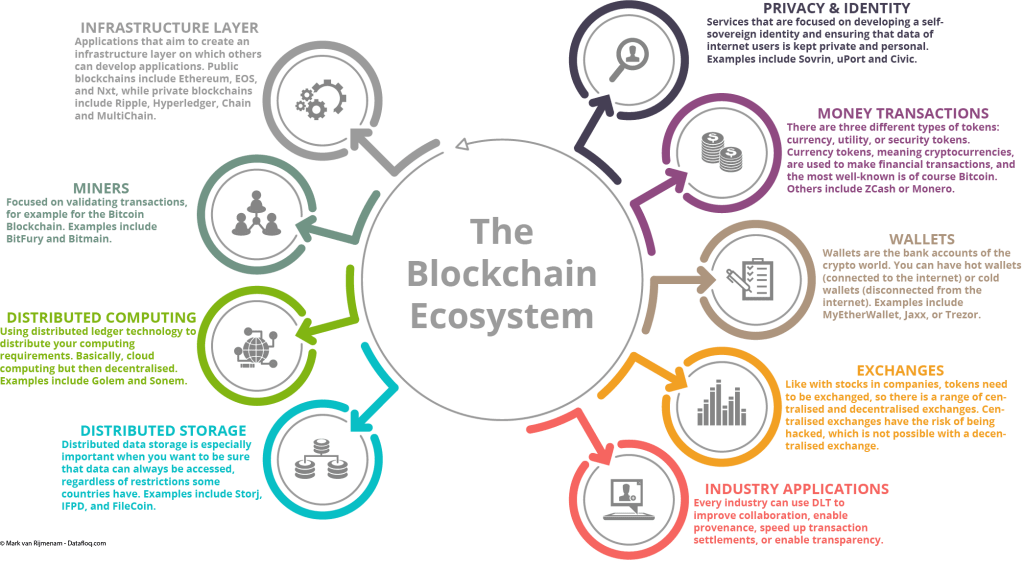
Source: thedigitalspeaker.com
Expert Level Questions on Blockchain
Q 1. What is Double Spending? Is it Possible to Double-spend in the Blockchain Ecosystem?
Double spending is when a digital asset, such as a cryptocurrency, is spent more than once. This is a problem in traditional digital payment systems because there is no way to prevent a user from copying a digital asset and sending it to two different recipients.
In a blockchain ecosystem, double spending is prevented by the consensus mechanism used by the network. For example, in a Proof of Work blockchain, transactions are verified and added to the blockchain in blocks, and a new block is added to the chain approximately every 10 minutes. This means that once a transaction has been confirmed and added to a partnership, it is tough to change the state of the blockchain and double-spend the asset.
However, it is technically possible to double-spend in a blockchain ecosystem, but it isn’t easy and requires a significant amount of computational power. For example, in a Proof of Work blockchain, an attacker must control over 50% of the network’s computing power to perform a 51% attack and double-spend an asset.
In conclusion, while double spending is a concern in traditional digital payment systems, it is primarily prevented in a blockchain ecosystem by the network’s consensus mechanism and decentralized nature.
Q2. What Kind of Records can be Kept in Blockchain? Is there any Restriction to the Same?
Blockchain technology is not limited to any specific type of data or record-keeping. In theory, any data that can be represented digitally can be recorded on a blockchain. In practice, blockchains are most commonly used to keep records of financial transactions, such as cryptocurrency transfers, but they can also be used for other types of data, such as:
- Supply chain Management: Blockchains can be used to track the movement of goods and materials through a supply chain, providing a transparent and immutable record of each step in the process.
- Digital Identities: Blockchains can store and manage digital identities, providing a secure and decentralized way to store personal information.
- Medical Records: Blockchains can store and manage medical records, providing a secure and transparent way to access and share health information.
- Property Records: Blockchains can be used to store and manage property records, providing a secure and transparent way to track the ownership of assets.
There is no inherent restriction on the type of data that can be recorded on a blockchain. Still, the specific data that can be stored on a particular blockchain depends on the design and specifications of that blockchain. In general, blockchains are best suited for data that needs to be secure, transparent, and tamper-resistant and where multiple parties need access to the same information.
Q3. Which Cryptographic Algorithm is Used in Blockchain?
Blockchain technology uses cryptographic algorithms to secure the data and maintain the ledger’s integrity. The specific cryptographic algorithm used in blockchains depends on that blockchain’s design and specifications. Some of the most commonly used cryptographic algorithms in blockchain technology include:
- SHA-256 (Secure Hash Algorithm 256-bit): This hash function is used in many blockchains’ Proof of Work consensus mechanism, including Bitcoin. It is used to secure transactions and ensure they cannot be tampered with.
- Elliptic Curve Digital Signature Algorithm (ECDSA): This is a digital signature algorithm used in many blockchains, including Bitcoin, to sign transactions and provide a secure way to verify the sender’s identity.
- Scrypt: This is an essential derivation function used in some alternative cryptocurrencies, such as Litecoin, to secure transactions and prevent using specialized hardware (ASICs) in mining.
- Ethash: This is a hash function used in the Ethereum blockchain to secure transactions and maintain the ledger’s integrity.
- Blake2b: This is a hash function used in some alternative cryptocurrencies, such as Siacoin, to secure transactions and prevent using specialized hardware (ASICs) in mining.
In conclusion, various cryptographic algorithms are used in blockchain technology to secure the data and maintain the integrity of the ledger. The specific algorithm used depends on the design and specifications of the blockchain.
Source: tutorialandexample.com
Q4. What are the Benefits of Blockchain?
Blockchain technology offers several benefits, including:
- Decentralization: Blockchains are decentralized networks that do not rely on a central authority to validate transactions. This makes them more secure and resistant to censorship, fraud, and tampering.
- Transparency: Blockchains are transparent by design, meaning that all participants in the network have access to the same information. This makes it possible to create trust between parties without a central authority.
- Immutable: Once a block is added to a blockchain, it cannot be altered or deleted. This makes blockchains ideal for storing data that needs to be secure and tamper-resistant, such as financial transactions or medical records.
- Security: Blockchains use cryptographic algorithms to secure the data and maintain the ledger’s integrity. This makes them very secure and resistant to hacking and cyber-attacks.
- Cost savings: By removing the need for intermediaries and reducing the costs of transactions, blockchains can significantly reduce costs for businesses and individuals.
- Efficiency: By eliminating the need for intermediaries, blockchains can streamline processes and make transactions faster and more efficient.
- Interoperability: Blockchains can create a common platform for different systems and technologies to interact, reducing the friction and costs of cross-border transactions.
In conclusion, blockchain technology offers several benefits, including decentralization, transparency, immutability, security, cost savings, efficiency, and interoperability, making it a promising technology for various industries and applications.
Q5. What do you mean by Coin-base Transaction?
A coinbase transaction is a particular transaction in a blockchain that creates new cryptocurrency tokens. It is the first transaction in a block and is used to reward the miner who solves the cryptographic puzzle and adds the block to the blockchain. In other words, it is a transaction that generates new coins and adds them to the supply of the cryptocurrency.
The miner creates the coinbase transaction, typically the only transaction in a block that does not have a previous transaction as its input. Instead, it has unique information called a coinbase, which serves as a placeholder for the new coins being generated.
The coinbase transaction is an essential aspect of most proof-of-work-based systems, as it incentivizes miners to participate in the network and secure the blockchain. The reward for mining a block can come from a block subsidy, transaction fees, or both.
Conclusion
Well, I hope you were able to understand today’s reading! If you were able to answer all the questions, then bravo! You are on the right track toward your preparation; if not, there’s no need to be concerned. The real value of today’s blog would come up if you can absorb these concepts and then apply them to the questions you would be facing in your interviews.
To summarize for you, the key takeaways of today’s articles would be:
- To understand blocks, the different types of blockchains and their key features
- Encryption and its role in blockchain
- Merkle Trees and how it is used in blockchain technology
- The concept of the ledger and how the ledger of blockchains is different from the shared ledger
- The other components of a blockchain
- The idea of double-speeding and using double speeding in the blockchain environment
- Record-keeping in blockchain
- The cryptographic algorithm of blockchain
- The benefits of blockchains and coin-base transaction
If you go through these thoroughly, I can ensure that you have covered the length and breadth of blockchain. The next time you face similar questions, you can confidently answer them! I hope you found this blog helpful and that I successfully added value to your knowledge. Good luck with your interview preparation process and your future endeavors!
The media shown in this article is not owned by Analytics Vidhya and is used at the Author’s discretion.