Introduction
In the ever-evolving landscape of cloud computing, ensuring your AWS resources’ security, compliance, and overall health is paramount. This is where AWS Config steps in as a crucial ally. AWS Config is a powerful service provided by Amazon Web Services that enables you to maintain a comprehensive and up-to-date record of your AWS resource configurations and changes over time. By capturing a detailed inventory of your resource settings and relationships, AWS Config provides valuable insights into your environment’s compliance, security posture, and operational health. This article delves into the functionalities and benefits of AWS Config, shedding light on how it empowers organizations to enhance their governance, mitigate risks, and ensure the best practices in their cloud infrastructure.
This article was published as a part of the Data Science Blogathon.
Table of contents
Introduction to AWS Config
It can be easy to forget alerts in your AWS account’s health dashboard, even though you might want to check one particular alert. In particular, if you use AWS Config, the upcoming September 15, 2021, changes may stop supporting your cloud architecture components. Let’s take a look at the AWS statement below:

As part of our ongoing effort to optimize the costs associated with recording changes related to certain transient workloads, AWS Config is scheduled to release an update to relationships modeled within configuration items (CI) for 7 types of EC2 resources on September 15, 2021. Examples of transient workloads include changes to Amazon Elastic Compute Cloud (Amazon EC2) Spot Instances, Amazon Elastic MapReduce jobs, and Amazon EC2 Autoscaling. This update optimizes CI models for EC2 instance resource types, Security Group, Network Interface, Subnet, VPC, VPN Gateway, and Customer Gateway to record direct relationships and discard indirect relationships.
While you’ll find a breakdown of the announcements here, we’ll cover the basics of AWS Config, dive into upcoming changes, and offer examples of solutions your organization can implement throughout this post.
Benefits of Using AWS Config
AWS Config offers these advantages, enhancing resource management, compliance, security, and overall governance within your AWS environment:
| Continuous Visibility | Monitor resource state and changes in real-time. |
| Resource Inventory | Maintain an automated inventory of AWS resources. |
| Change Tracking | Track configuration changes and their history. |
| Compliance Monitoring | Evaluate resources against predefined rules. |
| Automated Remediation | Automatically correct non-compliant resources. |
| Security Analysis | Identify security vulnerabilities and misconfigurations. |
| Customizable Rules | Create rules tailored to your organization’s needs. |
| Historical Analysis | Analyze past events for troubleshooting and auditing. |
| Multi-Account Governance | Enforce policies across multiple AWS accounts. |
| Resource Relationships | Understand dependencies and associations. |
| Notifications and Alerts | Receive notifications on configuration deviations. |
| Evidentiary Support | Comprehensive record for audits and investigations. |
AWS Config Rules
AWS Config Rules are a powerful feature of AWS Config that allow you to define and enforce specific desired configurations and compliance policies for your AWS resources. These rules help you maintain the desired state of your resources and ensure that they adhere to specific guidelines.
- Rule Definition: AWS Config Rules are defined using AWS Lambda functions or predefined rules provided by AWS. They evaluate the compliance of your resources against desired configurations.
- Real-Time Evaluation: Config Rules continuously monitor your resources in real-time, assessing their compliance against the specified configurations. An AWS Config non-compliance event is triggered if a resource violates a rule.
- Customizable: You can create custom rules using AWS Lambda functions tailored to your organization’s requirements. This allows you to define complex compliance checks beyond the scope of managed rules.
- Managed Rules: AWS also provides a set of managed rules covering common compliance requirements. These rules are preconfigured and can be easily applied to your resources.
- Automated Remediation: Some AWS Config Rules can automatically trigger remediation actions to bring non-compliant resources back into compliance. This helps maintain the desired state of resources without manual intervention.
- Notifications: AWS Config can send notifications when a rule is triggered or a resource becomes non-compliant. These notifications can be sent via Amazon SNS or Amazon CloudWatch Events.
- Integration with AWS Organizations: Config Rules can be used to enforce compliance policies across multiple AWS accounts in an AWS Organization.
- Scalability: AWS Config Rules can scale to handle large numbers of resources across your AWS environment.
Configuration Concept
As you may know, AWS Config allows you to track current and historical resource configurations in your AWS account. AWS Config takes a snapshot of your deployed resources’ settings and stores them in a configuration item, which AWS refers to as a record of the settings of your specific resources at a specific time. These can be generated immediately when your resources are updated or on a schedule, such as every six hours.
A configuration item represents a point-in-time view of various attributes of a supported AWS resource in your account. Configuration item components include metadata, attributes, relationships, current configuration, and related events. AWS Config creates a configuration item whenever it detects a change in the type of resource it records. For example, if AWS Config logs Amazon S3 buckets, AWS Config creates a configuration entry whenever the bucket is created, updated, or deleted.
Example of Configuration of AWS Config
Configuration entries play a major role in AWS Config by serving as the source of truth for historical changes. AWS Config bases many things on these items; for example, when AWS Config gives you a timeline of the states of your resources, it uses configuration items in the background. This is how a configuration history of an I AM user looks. Each configuration item is represented by a gray rectangle highlighted in blue. Selecting one of these items can drill down into the relationships and changes associated with the AWS resource for the item’s timestamp.
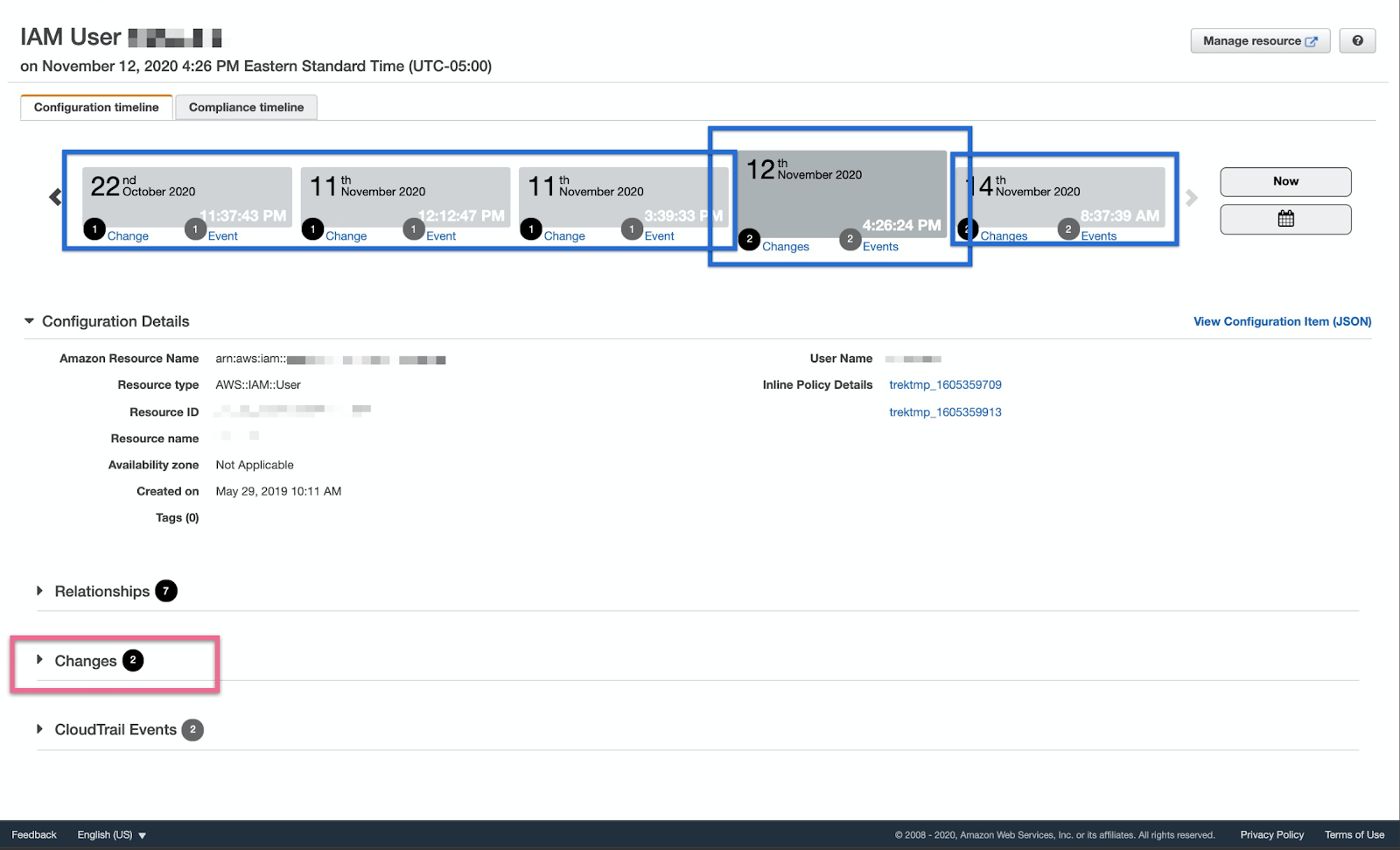
Using the above example, we can dive into the changes of the IAM user on November 12, 2020, by selecting the Changes dropdown menu in the pink box above.
CLI AP
AWS Config creates configuration items with the same API calls as the AWS CLI. Specifically, they use CLI list and describe commands such as AWS ec2 describe_instances –filters Name=tag-name, Values=example-tag. For each configuration item created, AWS Config can make multiple API calls.
Types of relationships:
- Direct
- Indirect Relationships.
A direct relation is the one returned when the Describe API is called. For example, the security groups attached to the instance are returned when AWS Config [makes] the Describe Instances call.
An indirect relationship is not returned when you call the Describe API. This requires multiple calls to Describe. For example, when AWS Config calls [s] Describe Security Groups, the API call does *not* return* a list of instances to which the security group is attached. Config must make another API call to find this information. In short, the direct relationships of a resource configuration item can be created and documented using the description CLI command of the same resource service. On the other hand, indirect relationships for a resource are relationships that AWS Config creates by calling another service’s description CLI API.
It can be confusing as to what is considered indirect and direct, so let’s dive into a specific example. Looking at the sample AWS configuration item timeline below, we’ve highlighted information for indirect relationships in pink and direct relationships in green; however, a useful rule of thumb is that if the information you want does not come from a CLI command that is bound to the resource you are referring to, then the information comes from an indirect relationship. Please note that when you call describe-security groups, we get information about the ingress/egress rules and the VPC the security lives in.
What is changing?
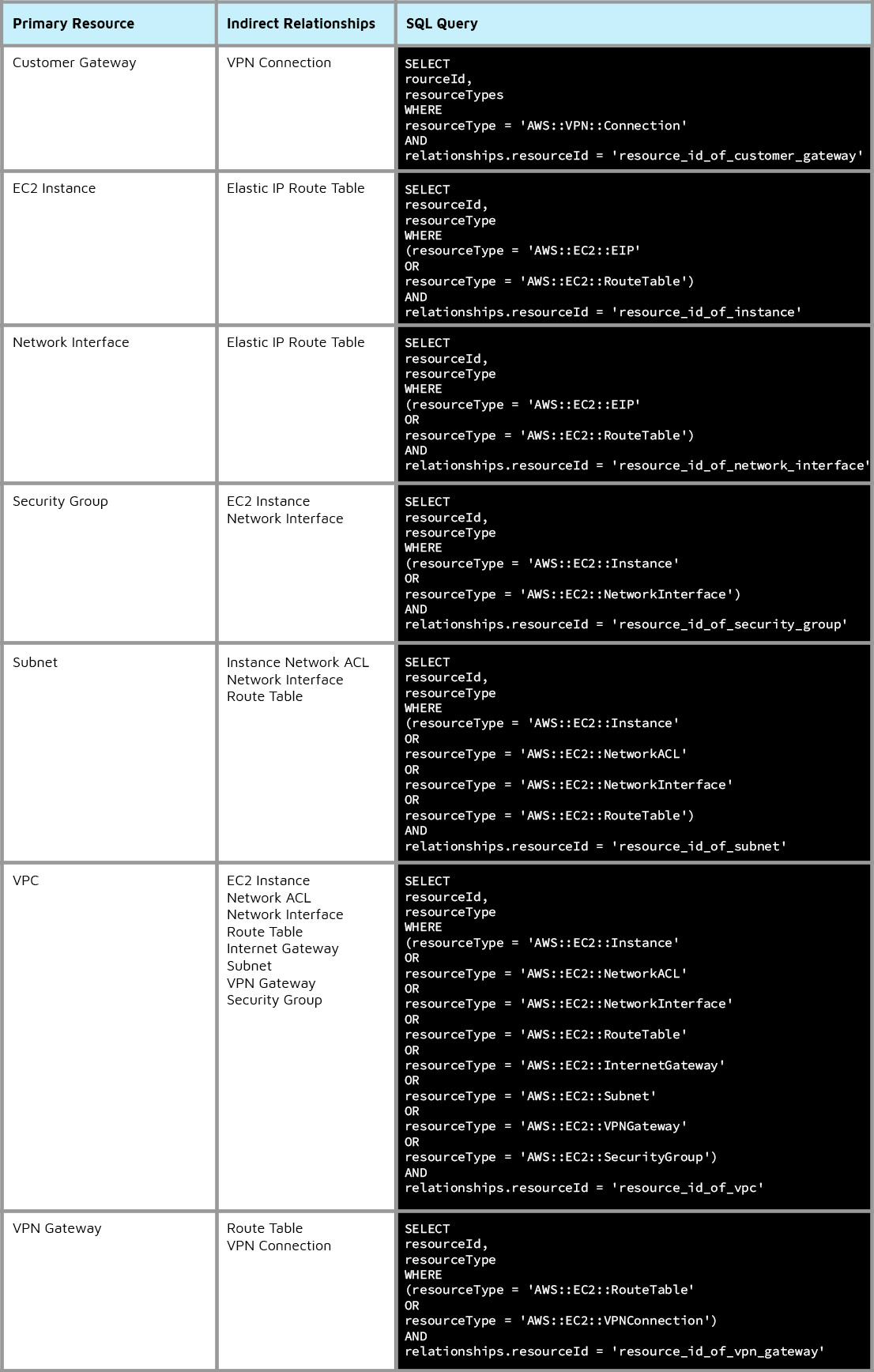
To increase the scalability of AWS Config, AWS reduces the number of API calls that AWS Config makes on the backend. Because of these changes, AWS will end support for calling indirect relationships for seven different resource types. Here is a list of the indirect relationships of the affected resources:
- Customer Gateway configuration items will no longer include VPN connections.
- EC2 instance configuration entries will no longer include EIPs or routing tables associated with an EC2 instance.
- Network interface configuration entries will no longer include the EIP or routing tables associated with the network interface.
- Security group configuration entries will not include attached EC2 instances or network interfaces.
- Subnet configuration entries will no longer include EC2 instances within the subnet, NACLs, network interfaces, and routing tables associated with the subnet.
- VPC configuration items will no longer include EC2 instances inside VPC, Internet gateways, NACLs, network interfaces, routing tables, subnets, security groups, and VPN gateways.
- Finally, VPN gateway configuration entries will no longer include associated routing tables or VPN connections.
To be clear, AWS has confirmed that there will be no impact on any current AWS configuration rules, only configuration items associated with resources. If you use AWS Config notifications for configuration item changes, this will affect you. Specifically, if you are using notifications for any of the above indirect relationship changes for your alerts or runbooks, your current setup will end on September 15, 2021.
Solution
If we need information for a rule currently configured, we can use AWS Config’s partially new advanced query feature to query this information using SQL. Using the example with security group sg-a1a1a1, we could see which EC2 instances are connected by either going to the EC2 console and manually checking each instance, or you can also use these queries.
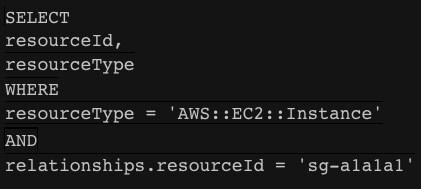
We’ve also expanded AWS’s documentation’s SQL queries to include additional queries to return indirect relationship information for the seven primary resources affected by upcoming AWS configuration changes.
Unfortunately, suppose you’re using SNS notifications for configuration item changes. In that case, this is a breaking change with no easy solution, so you’ll need to create your solution, such as spinning up a Lambda and generating the SNS notifications yourself.
AWS Config vs CloudTrail
| Feature | AWS Config | CloudTrail |
|---|---|---|
| Purpose | Tracks and manages resource configurations | Monitors and logs API activity |
| Coverage | Tracks configuration changes and compliance | Monitors API calls and events |
| Granularity | Granular details of resource configurations | High-level overview of API activity |
| Resource Types | Supports a wide range of AWS resource types | Focuses on API actions and events |
| Change Tracking | Tracks historical changes to resource configs | Logs API calls, including who and when |
| Compliance | Ensures resources adhere to desired settings | Assists with compliance auditing and analysis |
| Automation | Can trigger AWS Lambda functions for changes | Focuses on logging API events, not automation |
| Cost | Costs vary based on the number of resources | Costs based on data events logged |
Conclusion
AWS Config is scheduled to release an update to relationships modeled within configuration items (CI) for 7 types of EC2 resources on September 15, 2021. Examples of transient workloads include changes to Amazon Elastic Compute Cloud (Amazon EC2) Spot Instances, Amazon Elastic MapReduce jobs, and Amazon EC2 Autoscaling.
- AWS has confirmed that there will be no impact on any current AWS configuration rules, only configuration items associated with resources. This will affect you if you use AWS Config notifications for configuration item changes
- AWS Config takes a snapshot of your deployed resources’ settings and stores them in a configuration item, which is what AWS refers to as a record of the settings of your specific resources at a specific time.
- AWS reduces the number of API calls that AWS Config makes on the backend. Because of these changes, AWS will end support for calling indirect relationships for seven different resource types.
Frequently Asked Questions
A. AWS Config is a service that assesses, audits, and records configurations of AWS resources. It helps maintain compliance and security by continuously monitoring resource configurations for changes and assessing compliance against predefined rules.
A. While AWS Config and CloudTrail provide visibility into AWS resource activities, AWS Config focuses on resource configurations and changes over time. CloudTrail records API activity to track user actions and resource changes.
A. AWS Config Rules are customizable guidelines used to evaluate AWS resource configurations. They ensure that resources adhere to best practices and organizational policies, helping maintain compliance and security.
A. To run AWS Config, enable the service in your AWS Management Console, configure desired rules, and set up notifications. AWS Config will then continuously monitor and evaluate your resource configurations based on your defined rules.
The media shown in this article is not owned by Analytics Vidhya and is used at the Author’s discretion.