This article was published as a part of the Data Science Blogathon.
Introduction
The cloud comprises servers and a mix of networks, storage, service, and hardware, allowing businesses to save money and provide consumers with ease. Cloud is a collection of servers that can be accessed over the Internet, and all data is saved on physical servers in data centers. Through cloud computing, we may access actual servers and execute apps written in computer code on their devices. It enables users to access computer services from any device since processing and storage are performed on servers distributed across a knowledge Centre rather than locally on the user’s device. Email, online conferencing, and customer relationship management (CRM) are cloud-based applications.
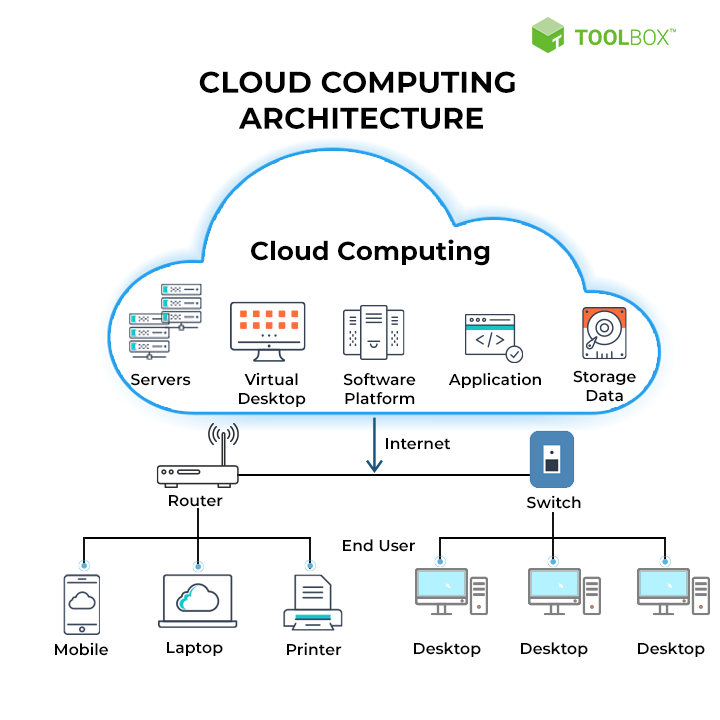
Cloud Computing is the remote manipulation, configuration, and use of hardware and software resources. It provides data storage, infrastructure, and application services online. As software is not required to be installed locally on the PC, cloud computing provides platform independence. Cloud computing, therefore, makes our business applications mobile and collaborative.
In comparison to traditional on-premises IT, cloud computing may assist with the following tasks, depending on the cloud services you choose:
-
Reduced IT costs: You may offload part or all of the expenses and work associated with acquiring, installing, configuring, and administering your on-premises infrastructure by using the cloud.
-
Increase agility and time-to-value: Instead of waiting weeks or months for IT to reply to a request, acquire and set up necessary gear, and install software, your business can start using enterprise apps in minutes using the cloud. You may also enable particular users, such as developers and data scientists, to help themselves to software and support infrastructure through the cloud.
-
Scale more easily and affordably: The cloud enables elasticity—rather than acquiring additional capacity that sits idle during quiet times, you may scale capacity up and down in response to traffic spikes and dips. You may also leverage your cloud provider’s worldwide network to bring your apps closer to people all around the globe.
Features of Cloud Computing
Major benefits can be gained by using cloud computing. Here are a few examples:
-
The installation of software is not required to access or operate cloud apps.
-
Cloud computing provides online development and deployment tools and a programming runtime environment through the PaaS concept.
-
Over the Internet, apps may be accessed as utilities.
-
The applications may be manipulated and configured online at any moment.
-
Cloud resources are available over the network platform independently for all client types.
-
Cloud Computing provides self-service on demand. The resources can be used independently of the cloud service provider.
-
Cloud Computing is extremely cost-effective due to its great operational efficiency and optimal use. It merely requires an Internet connection.
-
Cloud Computing provides load balancing, which increases its reliability.
Cloud Computing Interview Questions
1. What are the various deployment modes available on the Cloud?
The four modes are private, public, hybrid, and community cloud.
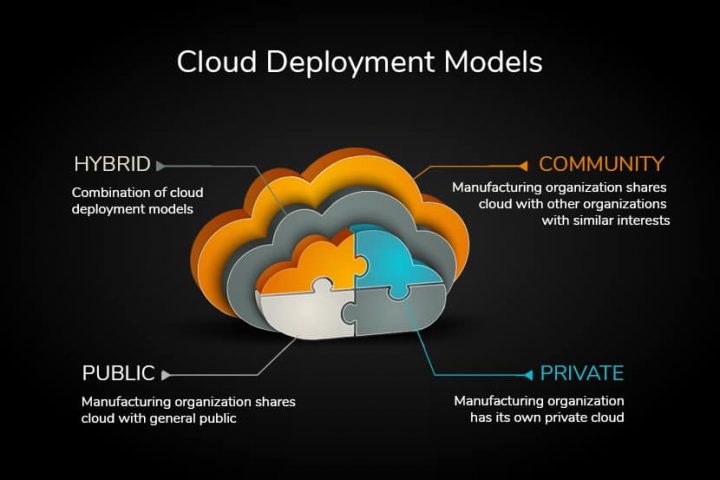
(Source: turningcloud.com)
-
Public – A public cloud is freely available to all users. Example: AWS Cloud Connect
-
Private – Private cloud is the aggregation of resources private organizations use for their purposes.
-
The community cloud enables multiple organizations within a group to access shared information, computing services, and systems.
-
Hybrid Cloud – The hybrid cloud combines private and public clouds that may shift from one to the other based on the circumstances and needs.
2. What is your understanding of the multi-cloud strategy?
The approach is not relying only on a single cloud service provider and distributes traffic among many cloud service providers. Different cloud providers may be exploited for their unique features, hence decreasing the workload of a single provider. This increases independence and reduces the chance of failure if the provider has technical difficulties or a traffic overload arises. Multi-cloud is a design used to administer the various cloud architecture from a single access point (portal). It may be as basic as a portal to oversee the functioning of all clouds.
3. What is the function of a hypervisor in Cloud Computing?
It is a virtual machine screen that can manage virtual machine resources logically. It allocates, splits, isolates, or modifies the virtualization hypervisor software. Hardware hypervisor enables concurrent operation of many guests operating systems on a single host machine.
Virtual Machine Manager is another name for it. Two kinds of hypervisors are described below:
-
Type 1: The guest Vm operates directly on the host hardware, like Citrix XenServer and VMware ESXi.
-
Type 2: The guest Vm operates on hardware through a host operating system, like Oracle Virtual Box or Vmware Player.
Type 1 Hypervisors are superior to Type 2 due to the absence of underlying middleware, which provides the optimal environment for mission-critical applications and workloads. To compare performance metrics, it is necessary to identify the CPU overhead, maximum host and guest RAM, and support for virtual processors.
4. Why are hybrid clouds so essential?
- The public cloud provides access capacity and specialized software, but not the private cloud.
- Examples: Virtual Amazon and Dynamo
- Hybrid clouds combine the advantages of both worlds.
vCloud:
- It is a cloud from VMware.
- It is a costly item.
- It provides enterprise quality.
OpenStack:
- It is less trustworthy.
- OpenStack supports web server operation.
- The database is constructed on vCloud.
5. What security advantages can cloud computing offer?
Complete defense against DDoS attacks: Distributed Denial of Service attacks has grown widespread and are now targeting cloud-based company data. Therefore, cloud computing security restricts traffic to the server, preventing threats to the organization and its data. Data Security: Data breaches become a serious concern as data grows and servers become soft targets. The cloud data security solution safeguards critical information and protects the data against unauthorized access.
Flexibility: Cloud provides flexibility, which contributes to its widespread use. The user can prevent server failure in the event of heavy traffic. When peak traffic has subsided, the user may cut down to save expenses.
The application server used for identity management is authorized by cloud computing. It allows users to manage the access of another user accessing the cloud environment.
6. What exactly is a cloud VPN?
Cloud VPN enables businesses to migrate their VPN services to the cloud. Available VPN services include Remote Access and Site-to-Site connections.VPN equipment is installed locally in the business network in a Site-to-Site connection. This equipment connects to a cloud-based virtual VPN endpoint. The VPN creates a tunnel between the cloud and the organization. This connection is similar to a physical connection and does not need a public IP address.
Remote Access allows users to connect to equipment in other parts of the world. For instance, VPNaaS.
In the connection logic, users install VPN software on their devices and establish a connection to a cloud VPN. The cloud VPN forwards the connection to the concerned SaaS application.
7. What is the distinction between mobile computing and cloud computing?
Cloud Computing involves storing your files and folders on the Internet’s “cloud.” This will enable you to access your files and folders from anywhere globally; however, you will need a device with Internet connectivity. Mobile computing entails taking a physical device, like a laptop, mobile phone, or other devices. Mobile computing and cloud computing are comparable, and mobile computing employs the cloud computing paradigm. Cloud computing provides consumers with the necessary data. In contrast, mobile computing apps operate on a remote server and allow users access to data storage and management.
8. Mention the basic AWS elements.
The basic AWS elements are as follows:
-
AWS Route 53 is a DNS (Domain Name Server) web-based service infrastructure.
-
Simple Email Service: Emails are sent via a RESTFUL API call or conventional SMTP (Simple Mail Transfer Protocol).
-
Identity and Access Management: An AWS account is supplied with enhanced security and identity management.
-
Simple Storage Service (S3): It is a massive storage media used extensively by AWS services.
-
Elastic Compute Cloud (EC2): It provides on-demand computing resources for hosting applications and is most suitable for workloads that are unexpected.
-
Elastic Block Stores (EBS): They are storage volumes connected to EC2 that extend the data retention period of a single EC2 instance.
-
CloudWatch: It is a service offered by Amazon. CloudWatch monitors AWS resources and enables managers to observe and obtain the necessary keys. Access is granted so that a notification alert may be triggered in the event of a problem.
9. How is Data protection accomplished in S3?
S3 supports encryption using SSE-S3, SSE-C, and SSE-KMS.
- SSE-S3 provides the solution S3 monitors Key management and protection via several security levels.
- SSE-C enables S3 to encrypt and decrypt data and manage the encryption key. AWS does not provide key management and storage since they are implementation-dependent.
- SSE-KMS uses the Amazon Key Management Service to store encryption keys. By retaining master keys, KMS adds an extra degree of protection. There is a need for special authorization to use the master key.
10. What differences exist between ELB, NLB, and ALB?
Application Load Balancer (ALB) – ALB enables port-based routing. Additionally, it may direct requests to Lambda and multiple ports on the target. Application Load Balancer only supports layer 7, which includes HTTP/2 and Web Sockets. It may return main replies independently, freeing the server from responding to duplicate requests. Microservices and applications use ALB. Network Load Balancer (NLB) –It supports Layer 4, which includes TCP and UDP. Since it is lower on the OSI model, it is more efficient and high-performance. It uses static IP addresses and may be allocated elastic IP addresses. Real-time data streaming and video streaming are examples.
Classic Load Balancer (CLB) or Elastic Load Balancer (ELB version1) – ELB is the oldest Load balancer and the only one that supports application-specific sticky session cookies. It works on both Layer 7 and Layer 4. ELB supports EC2-Classic as well.
Conclusion
This article describes cloud and cloud computing, which is an on-demand availability of computer system resources that uses clouds to provide services when the user wants them and provides access to a broader network of worldwide web servers. This page provides interview questions for all levels and covers the following areas as well:
- What are cloud computing and the cloud?
-
There are several deployment options available in the cloud.
-
Advantages of cloud computing for data protection and security
-
The contrast between mobile computing and cloud computing, as well as other areas.
The media shown in this article is not owned by Analytics Vidhya and is used at the Author’s discretion.